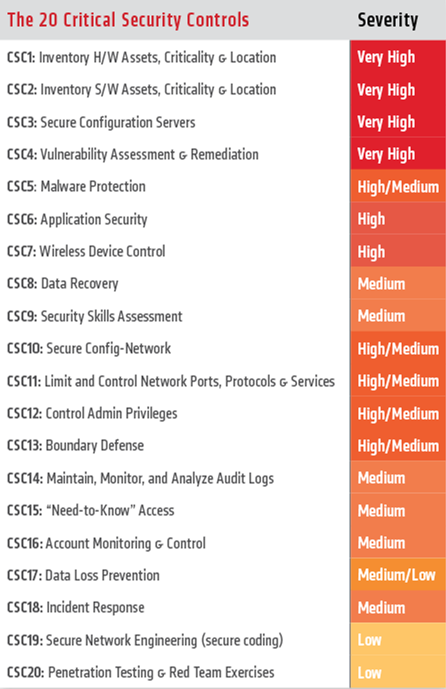
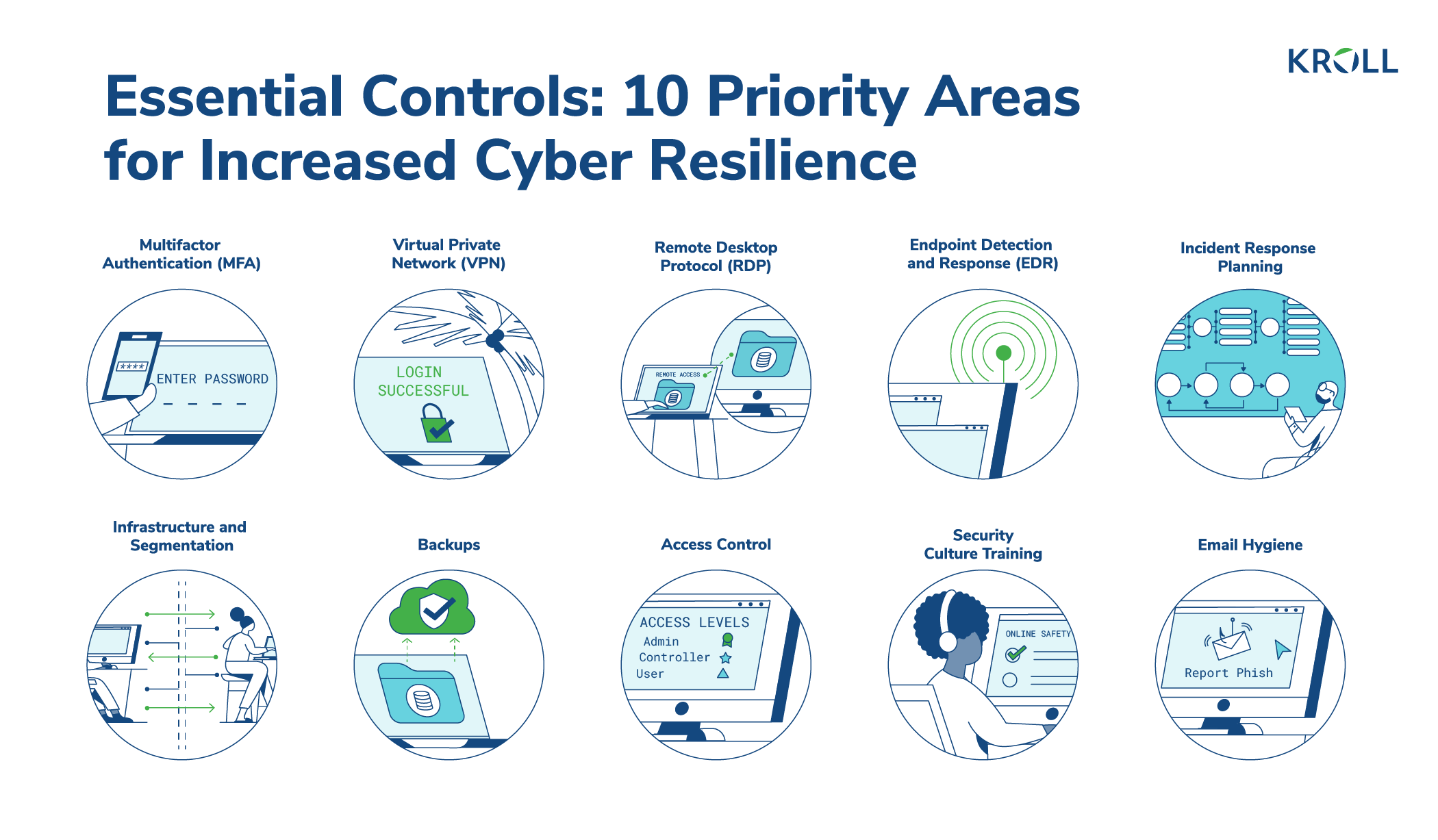
CISO-Level Guide: Protecting Your Organization - Cyber Resilience and Financial Organizations - Carnegie Endowment for International Peace
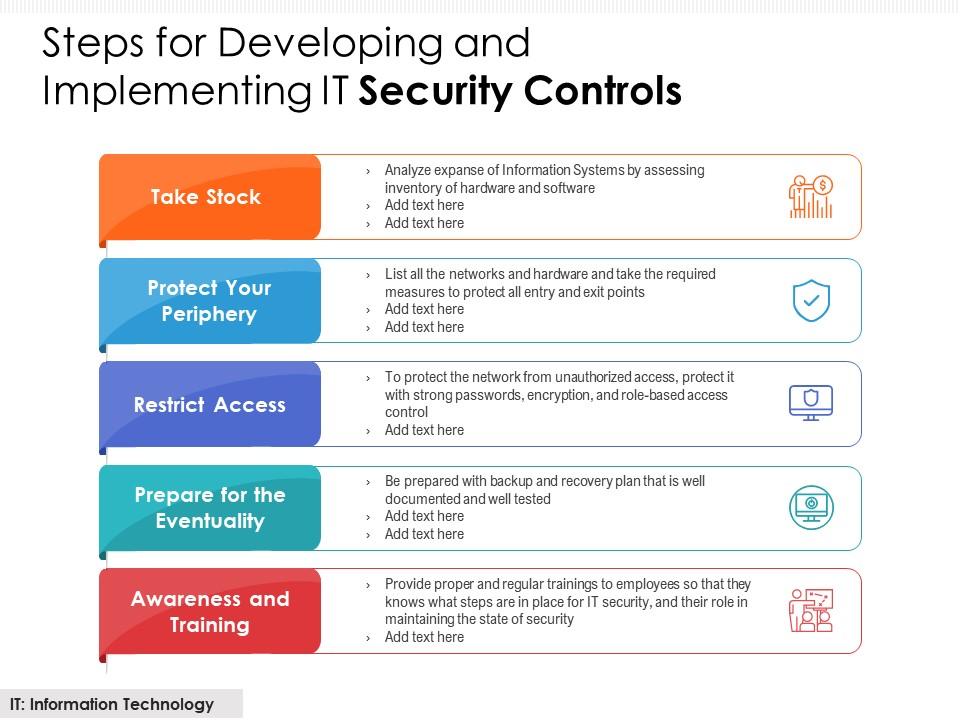
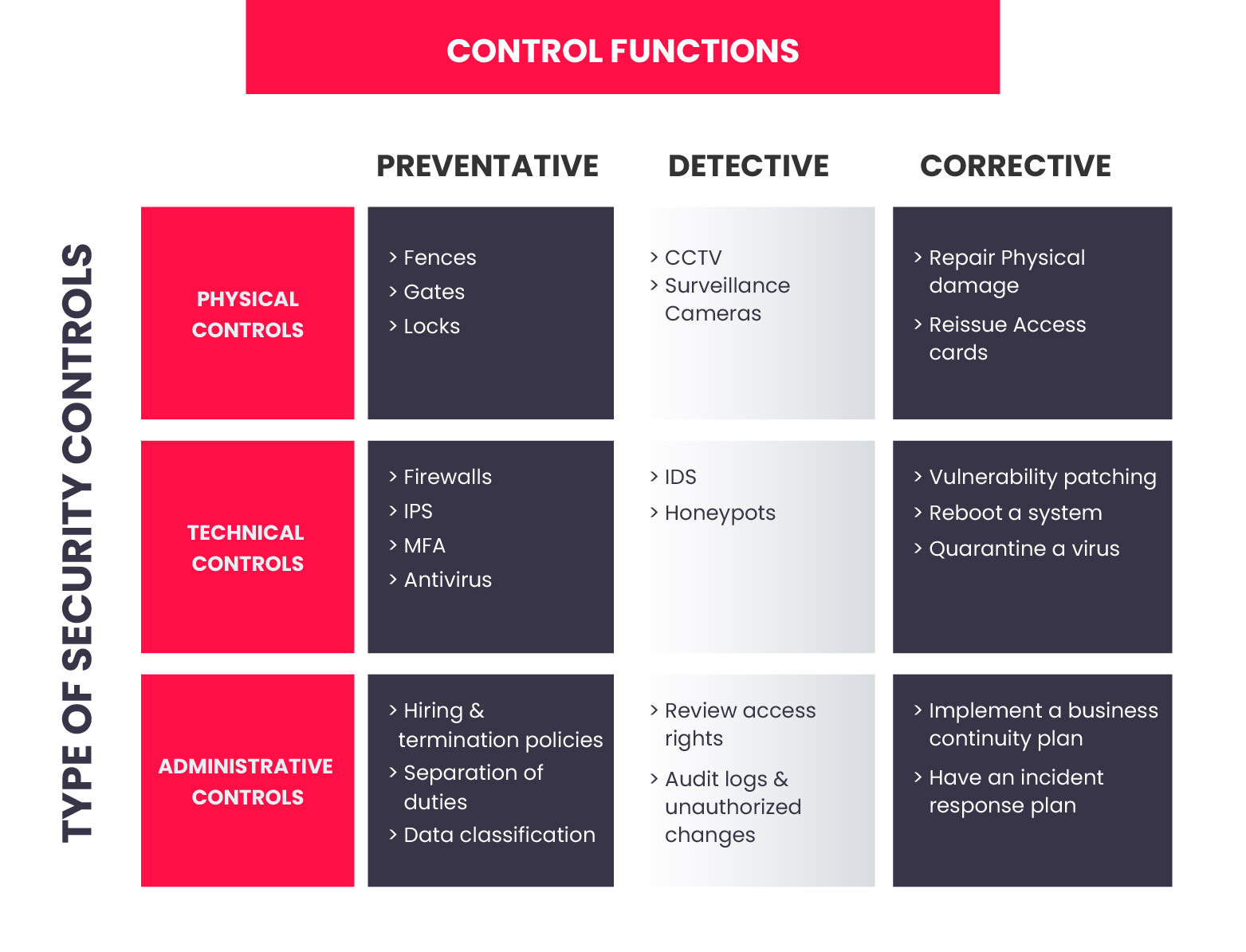
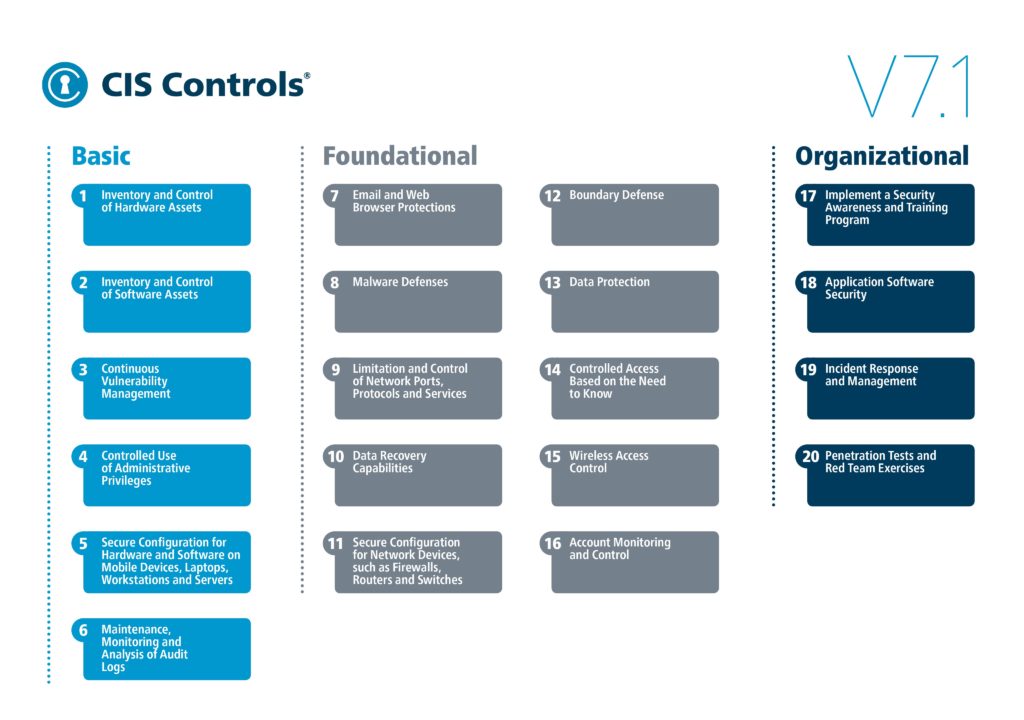
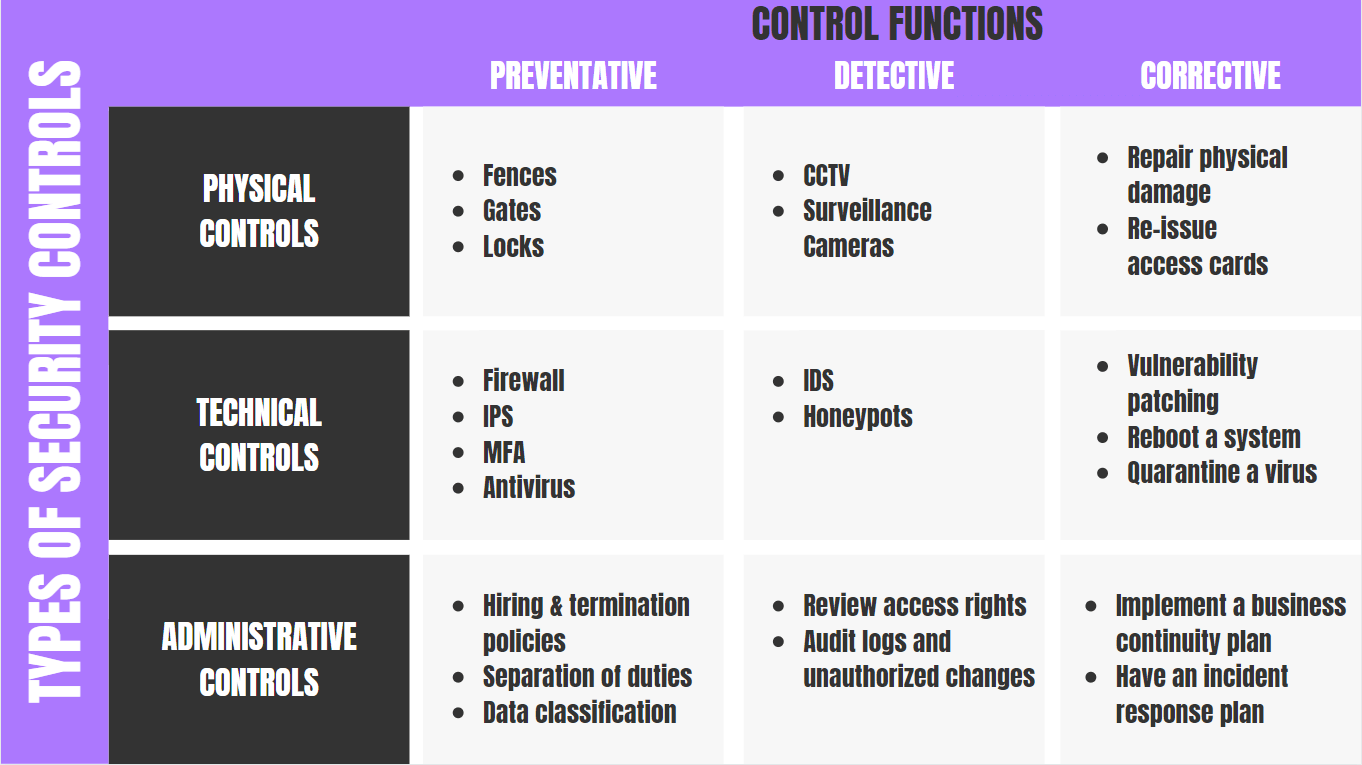
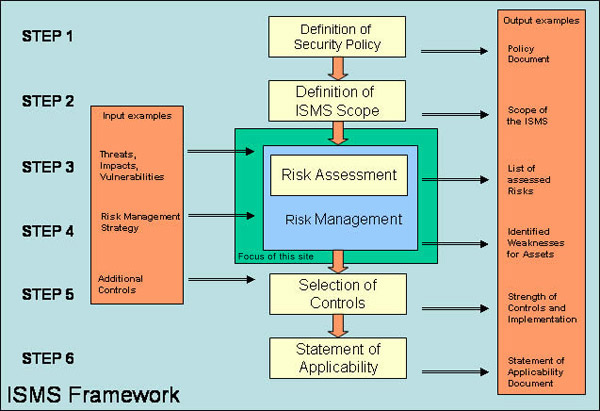
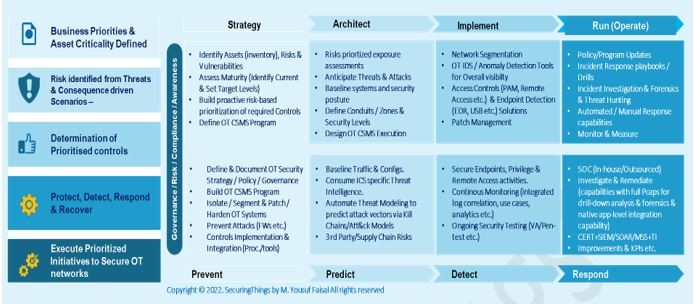
Steps For Developing And Implementing IT Security Controls | Presentation Graphics | Presentation PowerPoint Example | Slide Templates