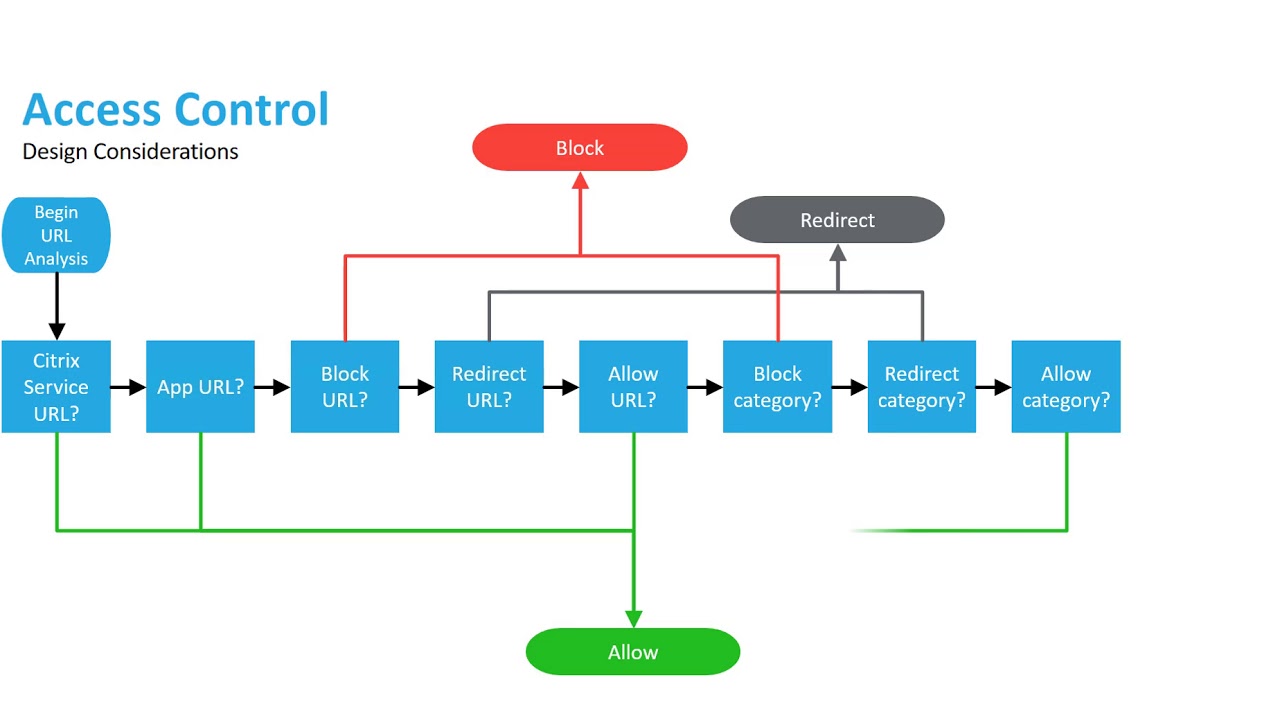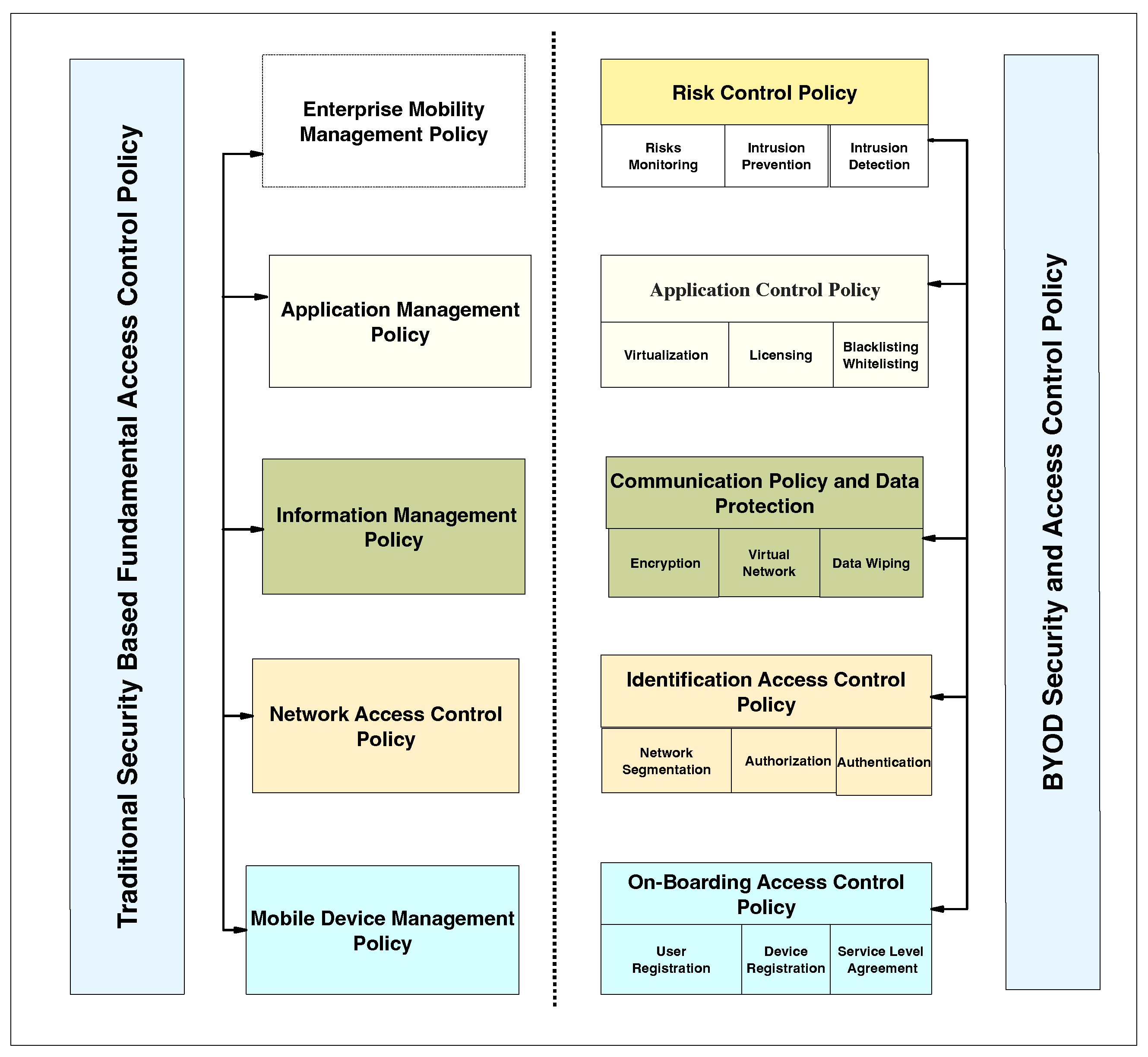
Applied Sciences | Free Full-Text | Systematic Literature Review on Security Access Control Policies and Techniques Based on Privacy Requirements in a BYOD Environment: State of the Art and Future Directions

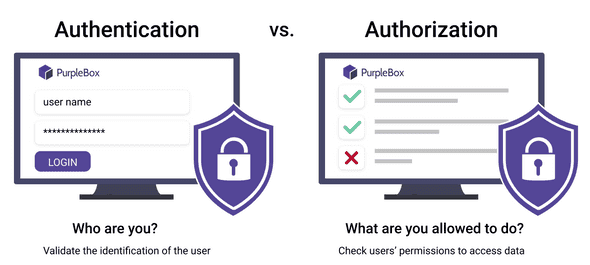
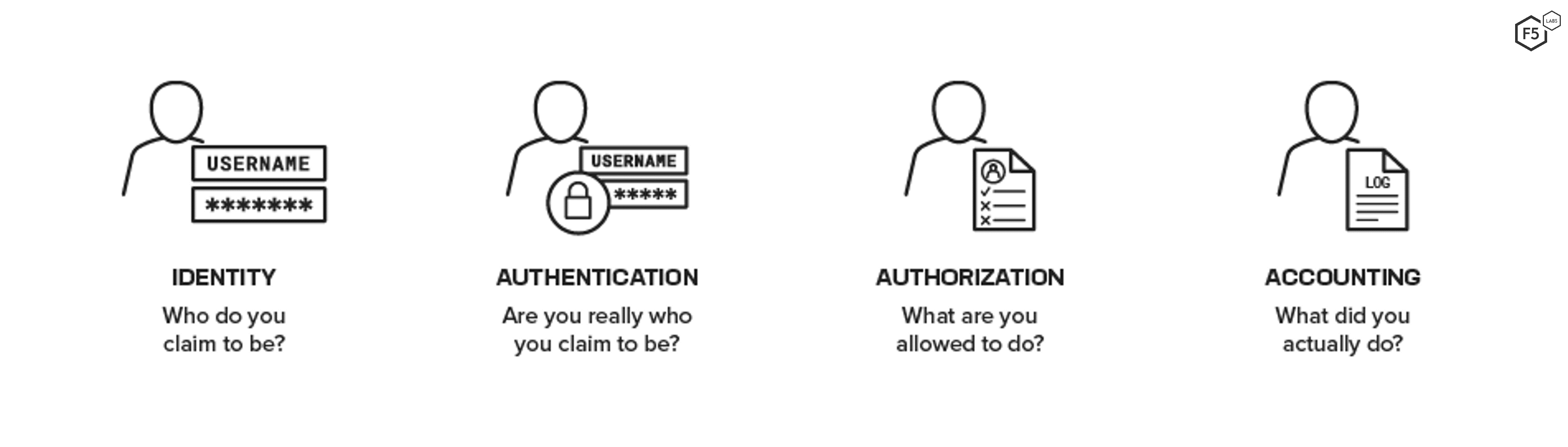
A Guide to Claims-Based Identity and Access Control: Authentication and Authorization for Services and the Web: Authentication and Authorization for Services, Web, and the Cloud : Baier, Dominick, Bertocci, Vittorio, Brown, Keith,